This is the second of five blog posts dedicated to the ‘Big 5′ Initiatives AwesomeCloud that is rolling out in 2013. This blog post focuses on the FortiGate Unified Threat Management (UTM) solution developed by Fortinet, which will be available to our Channel Partners during Q4 2013.
We opted to deploy UTM as a result of the feedback we have received from our partners. This feedback came from an informal survey that we conducted at the end of 2012 in order to identify and prioritize product improvements. As expected, cloud security emerged as an area where our partners expect AwesomeCloud to continue delivering ongoing improvements. We’re ratcheting up security and staying ahead of the cloud computing security curve by deploying UTM appliances in Q4 2013. If you’re wondering what UTM is and how your clients will benefit, keep reading.
What is Unified Threat Management (UTM)?
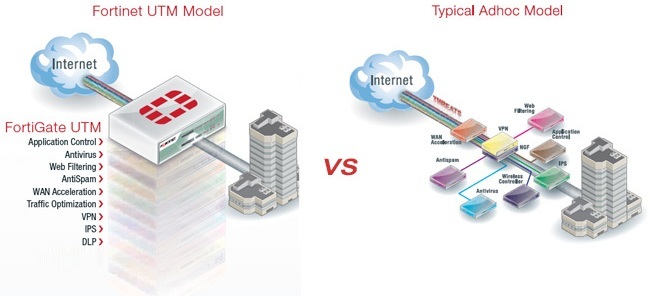
Unified Threat Management (UTM) is an all-in-one network security solution. UTM provides multiple security features (firewalling, intrusion prevention, anti-virus, etc.) without the complexity that comes with managing multiple security vendors. UTM has three characteristics that distinguish it from traditional network security:
- The ability to deploy, manage, and update network security from a centralized location instead of maintaining instances of security software on each client workstation.
- A cloud-based architecture that allows administrators to register and grant network access to specific computing devices. Granting access to specific devices extends the ability to deny access to specific devices without disturbing other users.
- Increased network performance by way of funneling data through a centralized security layer instead of through multiple security layers housed in different pieces of hardware.
With Unified Threat Management you’ll be able to deploy, manage, and update a comprehensive cloud-based security service for your clients without ever coming into physical contact with their computing devices.
How Can My Clients Benefit from Unified Threat Management (UTM)?
UTM gives you the opportunity to alleviate your clients’ security concerns by moving their security into the cloud. Clients leveraging UTM will spend more time focusing on their core competencies instead of dedicating resources to time-consuming security updates on individual devices.
In addition to helping your clients spend more time focusing on their strategy, UTM’s cloud architecture creates an added layer of security whereby network access depends on the device. Your clients can choose which devices are granted access to their network resources and the level of access that each device will receive. Finally, your clients’ network performance will improve as their security is centralized to the cloud.
Unified Threat Management (UTM) Solutions
Technology needs and solutions are unique to every organization. Accordingly, AwesomeCloud will offer an array of security options you can select for each of your clients. Every virtual UTM appliance will support the following core-security technologies:
- Application Control
- Anti-Virus
- Web Filtering
- Anti-Spam
- WAN Acceleration
- Traffic Optimization
- Remote user and site-to-site VPN
- Intrusion Protection (IPS)
- Data Loss Prevention (DLP)
- Two Factor Authentication
For more information about how the AwesomeCloud team is ratcheting up security, please drop us a line or post a comment below. You can also follow us on Twitter by using the @awecloud handle.






